An HTTP sniffer is a specialized type of network traffic analyzer for the HTTP protocol. It decodes HTTP(S) traffic (both requests and responses) and presents it in a human-readable form. This includes HTTP headers, cookies, request methods (GET, POST), URLs, status codes, response bodies, and more.
HTTP sniffers intercept traffic using one of several methods: network card promiscuous mode, proxy servers, or OS-level API hooks. Modern sniffers also support HTTPS decryption by acting as a MITM proxy with a temporary root certificate installation.
Unlike browser DevTools, an HTTP sniffer can capture all HTTP(S) traffic from any application on your system. This includes:
- - Debugging API issues
- - Inspecting authentication and header values
- - Diagnosing slow network responses

Types of HTTP Sniffers
- - Online HTTP Sniffers: Web-based tools that fetch a URL and display the response. Useful for basic checks only.
- - Proxy HTTP Sniffers: Capture traffic through a proxy server. Require proxy configuration and SSL certificate installation: Example Telerik Fiddler.
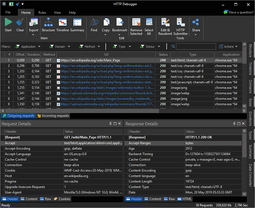
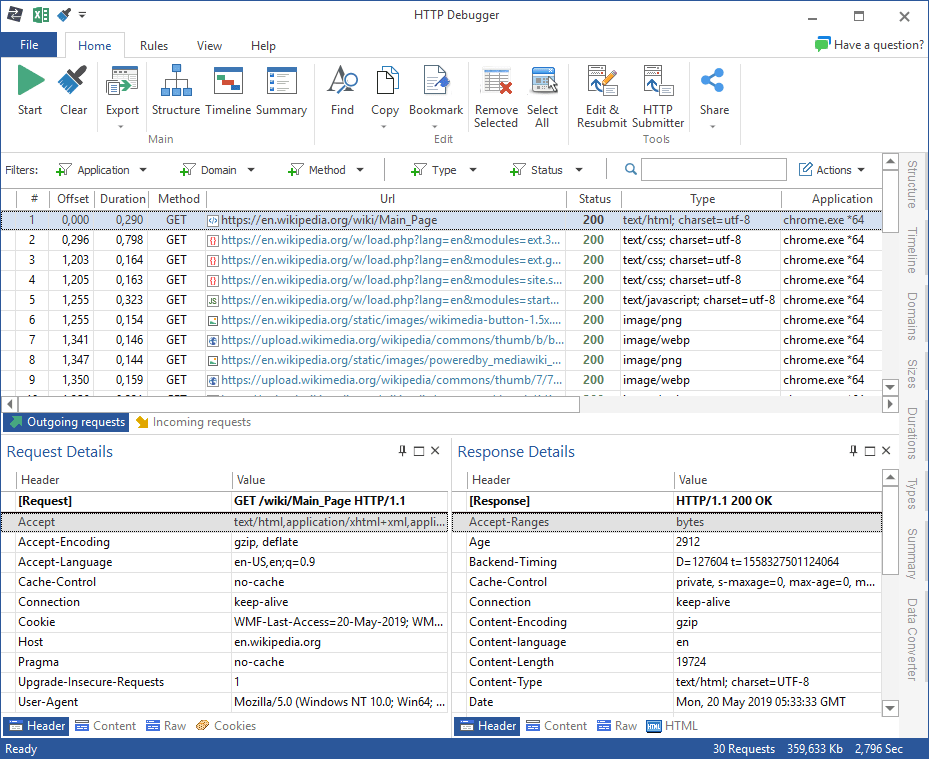
- - Application (Software) Sniffers: Capture all system HTTP/S traffic without proxy setup. Example: HTTP Debugger Pro.
HTTP Sniffers for API Developers
API developers benefit from advanced sniffer features like full request/response views, syntax-highlighted JSON, filtering, search, and the ability to replay and modify requests.
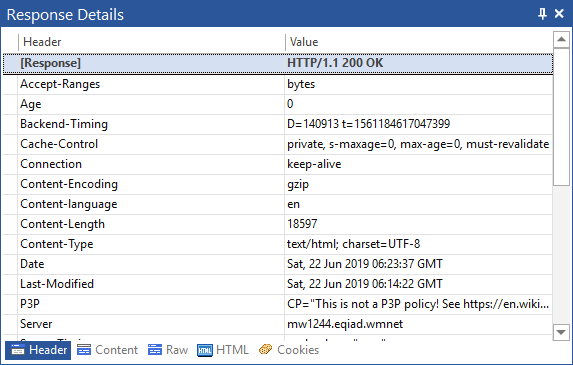
For example, HTTP Debugger Pro displays real-time HTTP traffic across the system. You can inspect:
- - Full request and response headers
- - POST data and query strings
- - API call payloads
HTTP Sniffers for Security and Network Administration
Administrators use HTTP sniffers to detect network anomalies, debug network issues, and trace security breaches. Use cases include:
- - Detecting malware communication over HTTP(S)
- - Analyzing suspicious headers or payloads
- - Monitoring HTTP status codes and performance bottlenecks
Conclusion
HTTP sniffers are powerful tools for developers and DevOps. They enable deep visibility into HTTP/S traffic, making debugging and security monitoring much easier. Tools like HTTP Debugger Pro simplify the entire process with a rich GUI, no proxy setup, and decoding SSL traffic out of the box.
Whether you're debugging a failing API call or tracking malware communication, HTTP sniffers provide the clarity needed to resolve problems fast.